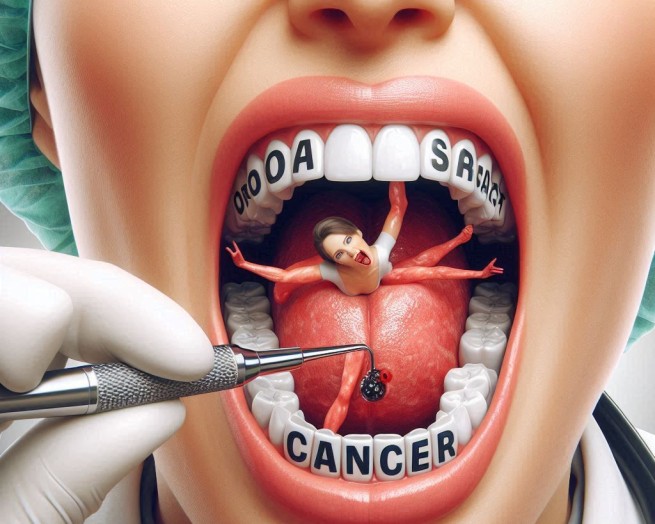
The black market for Covid-19 vaccines has been booming in recent months, flooding every corner of the so-called dark web and in the windows of illegal supermarkets ready for sale.
In fact, these are illegal, but quite standard electronic stores, where the buyer has the opportunity to choose from a variety of products, order what he wants by paying with money or cryptocurrency, and then receive his order from himself, as if you bought it on any regular Internet. -store.
And when we say that he can order whatever he wants, we mean that these stores sell everything from Covid-19 vaccines to drugs, weapons, explosives and stolen jewelry. Indicative is the fact that, according to official data, the demand for the purchase of such vaccines exceeded 400%!
The above has alerted authorities around the world as the drugs sold on the Darknet are of dubious quality, putting the health of those who end up using them in jeopardy.
As it turns out from the “visit” of these places, the buyer has the opportunity to order the vaccine from Moderna for $ 28. If he wants, he can buy the Pfizer vaccine for $ 39. In addition, the client has the opportunity, in addition to vaccines, to purchase hydroxychloroquine tablets (which is considered an extremely poisonous medicine for coronavirus), at a price of $ 60 per pack.
What is “Darknet”
Cannabis, heroin, weapons – anything for a rebellious soul
These are Internet sites, well protected from traditional search engines, in which drug and weapon dealers, criminals, thieves and other extreme lovers circulate.
To enter the “Darknet” and navigate illegal supermarkets, you need to use special software that will provide anonymity, effectively blocking digital traces.
This can be accomplished with the Tora, an onion-based browser. It should be noted that it was first created several years ago for the needs of the US Navy. The data passes through several Torus servers before reaching the outside world through the output server. The route between the Tor servers is chosen randomly for each new connection and changes every 10 minutes, but it can be forcedly changed. If you want to change the chain, update the connection. Data between servers is encrypted. However, the egress server, by definition, has access to the unencrypted data in transit. Tor is decentralized and open source. So, even if the United States wants to cut out its brainchild, it will no longer be able to. Open source guarantees trojan detection and forks.
Anonymity is achieved due to asymmetric encryption and forwarding messages from sender to recipient along the chain between nodes (servers-nodes of the chain). Each node has a certificate, which means that anyone can create a message encrypted in such a way that only the node for which it is intended can decrypt it. Nodes do not choose who to forward the message to. The entire route is laid before the sender himself sends messages. Moreover, none of the nodes knows the full route. Asymmetric encryption allows you to create secure keys for the “classic” symmetric, which is necessary to encrypt the instructions to the node, indicating to whom to forward the message further along the chain. Each node only knows from whom it received the message and to whom it should be transmitted further, since it uses only one key out of three. At least 3 nodes are always involved in sending a message. None of them know both the recipient and the sender at the same time. The first node only knows the sender. The last one is the recipient. Intermediate nodes only know their neighbors.




More Stories
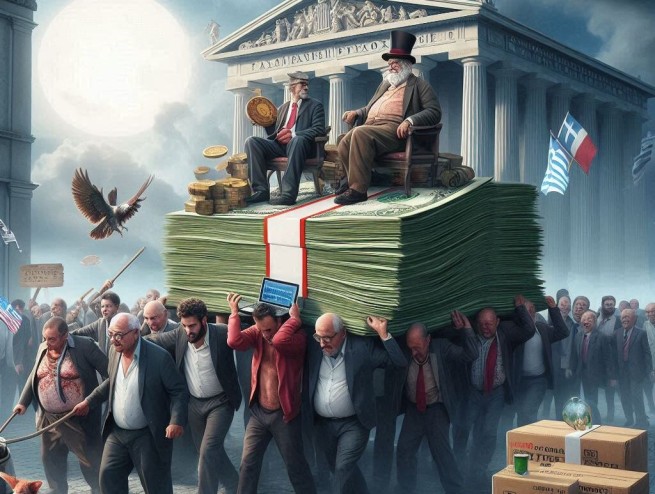
IOBE: Poverty threatens Greece
At what age does it start "third age"
After 2027, the retirement age will increase by another 1.5 years